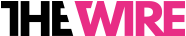
Fake permission requests are made to look like they are coming from Google Chrome
McAfee says, “While the app is installed, their malicious activity starts automatically. We have already reported this technique to Google and they are already working on the implementation of mitigations to prevent this type of auto-execution in a future Android version.”
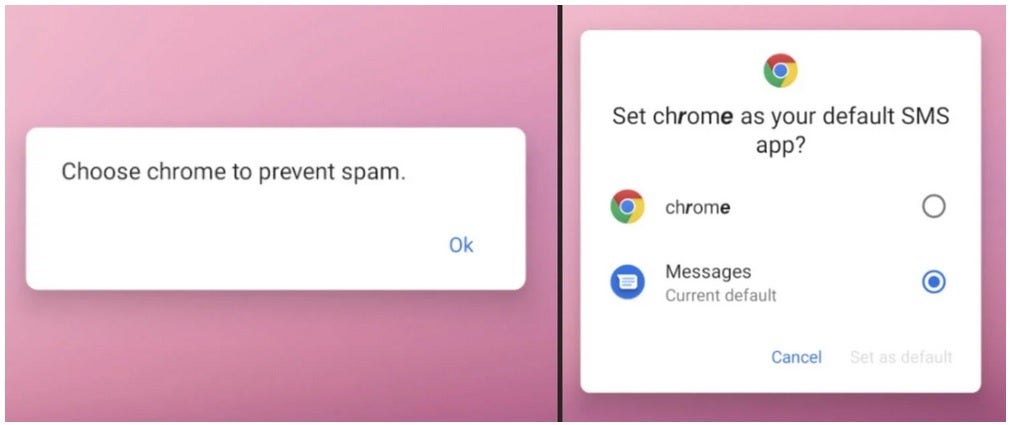
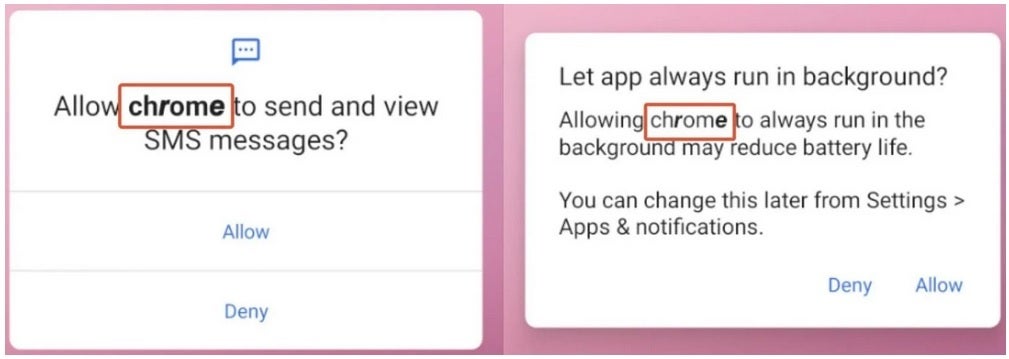
Another fake request for permission
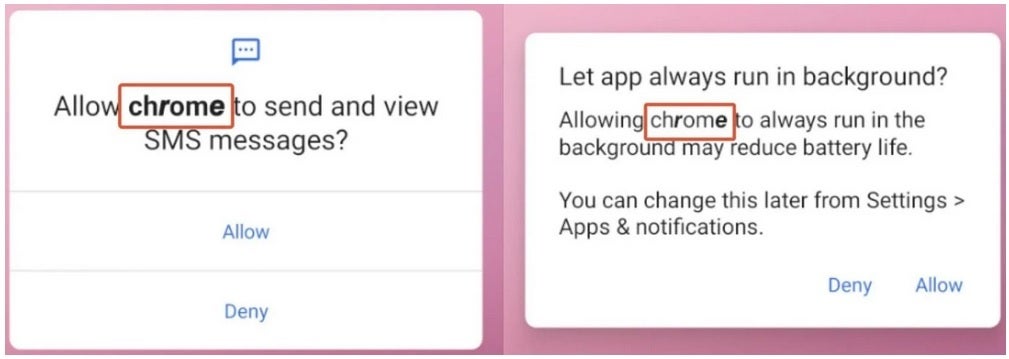
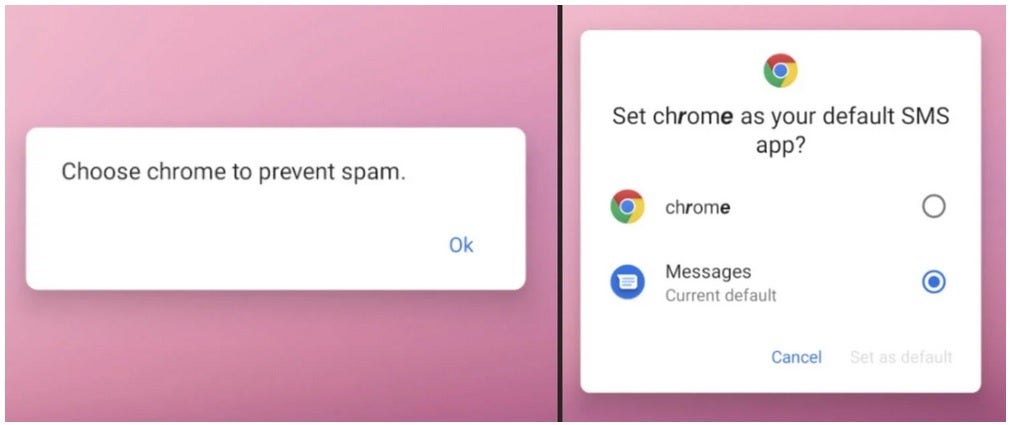
The malicious apps send out permission requests pretending to come from Google Chrome requesting permission to send and view SMS (text) messages and asking permission to keep “Chrome” running in the background. And the coup de grace is permission to make “Chrome” your default SMS app. The malware, once it gets all of these permissions, is used to send photos, text messages, contact lists, and info on the hardware you are using (including your phone’s unique IMEI number) to the control server. Yes, it is very scary.
McAfee says that since minimal interaction is required by the victim, the new XLoader malware is even more dangerous than its predecessor. There is some good news. An update from McAfee dated a couple of weeks ago says that Android devices with Google Play Services are protected from attacks from this kind of malware by Google Play Protect which is enabled by default.
Still, there are some takeaways to consider here. Never click on a shortened URL found in a message. And never sideload an app.
#Android #threat #sends #photos #texts #contacts #hardware #data #foreign #server